How to Use AWS Config to Monitor for and Respond to Amazon S3 Buckets Allowing Public Access | AWS Security Blog
How to Use AWS Config to Monitor for and Respond to Amazon S3 Buckets Allowing Public Access | AWS Security Blog

How to Use AWS Config to Monitor for and Respond to Amazon S3 Buckets Allowing Public Access | AWS Security Blog

How to Use AWS Config to Monitor for and Respond to Amazon S3 Buckets Allowing Public Access | AWS Security Blog

How to Use AWS Config to Monitor for and Respond to Amazon S3 Buckets Allowing Public Access | AWS Security Blog

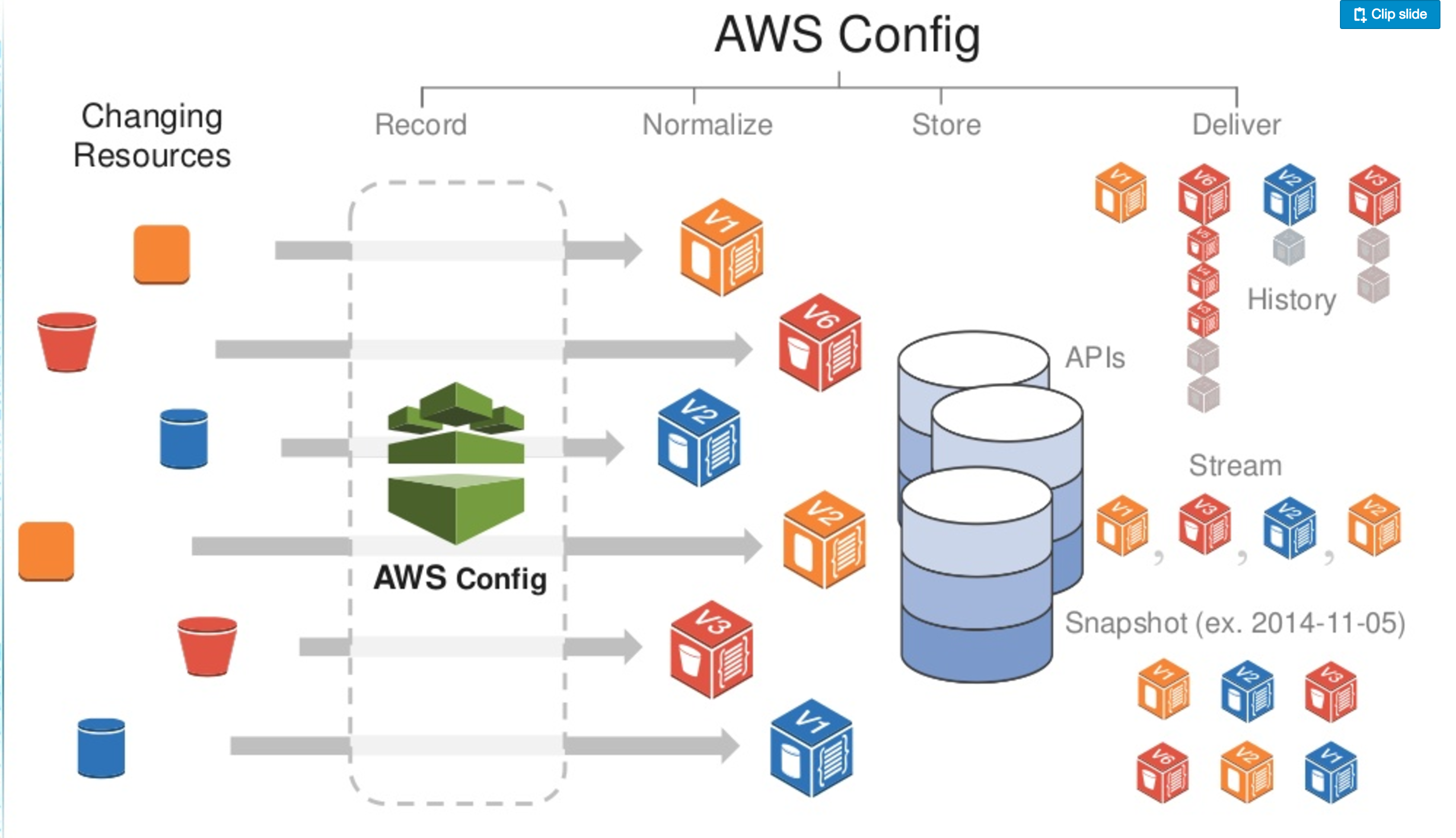
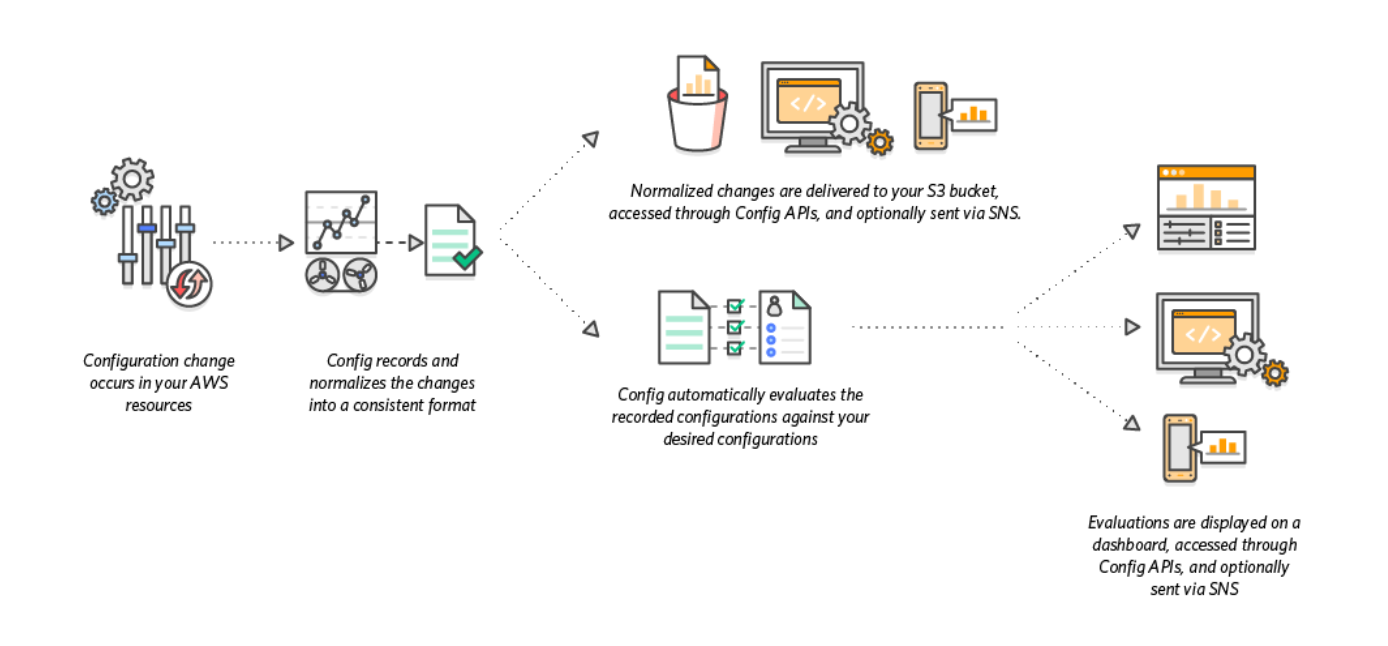
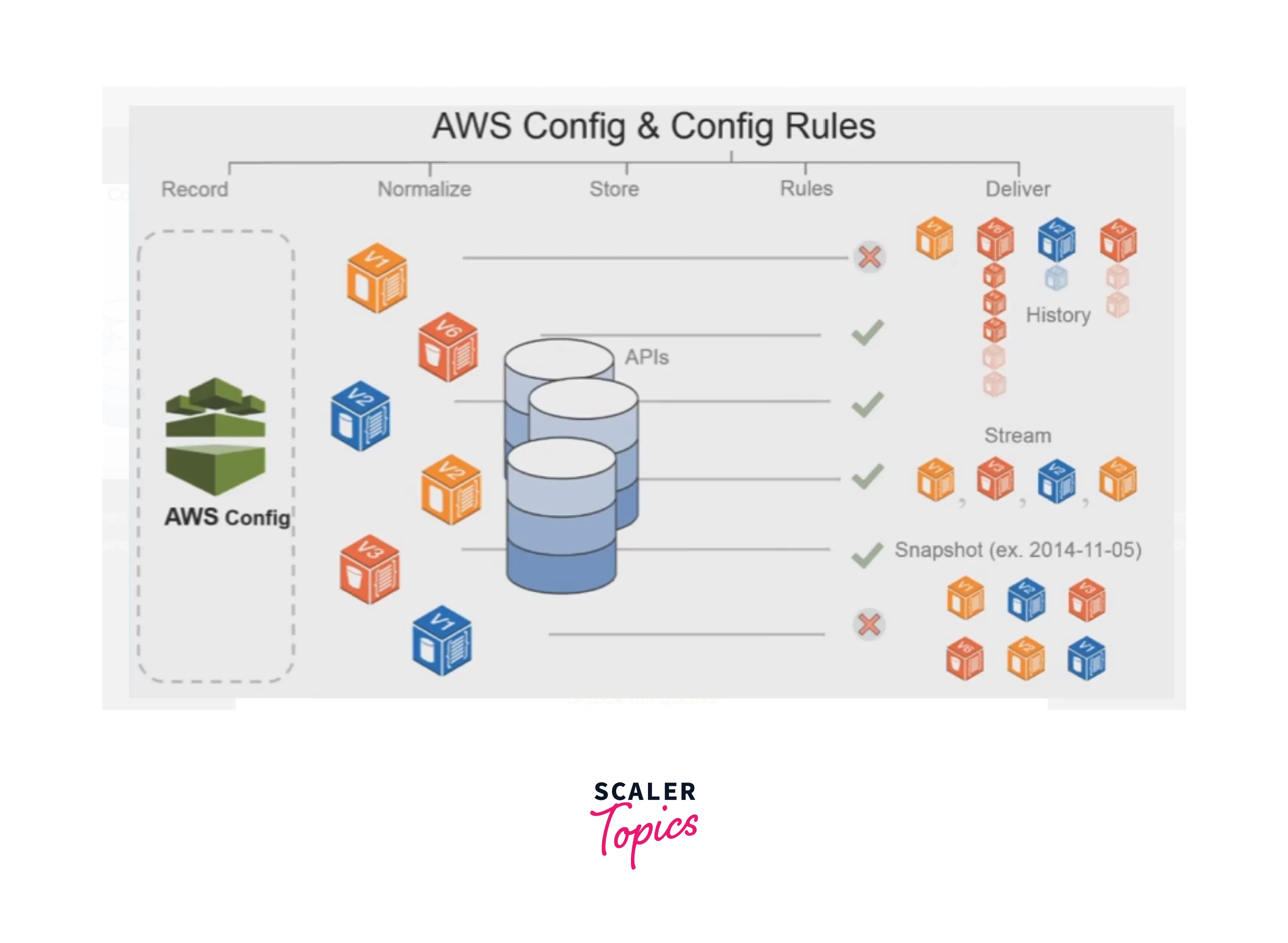
Understanding the differences between configuration history and configuration snapshot files in AWS Config | AWS Cloud Operations & Migrations Blog
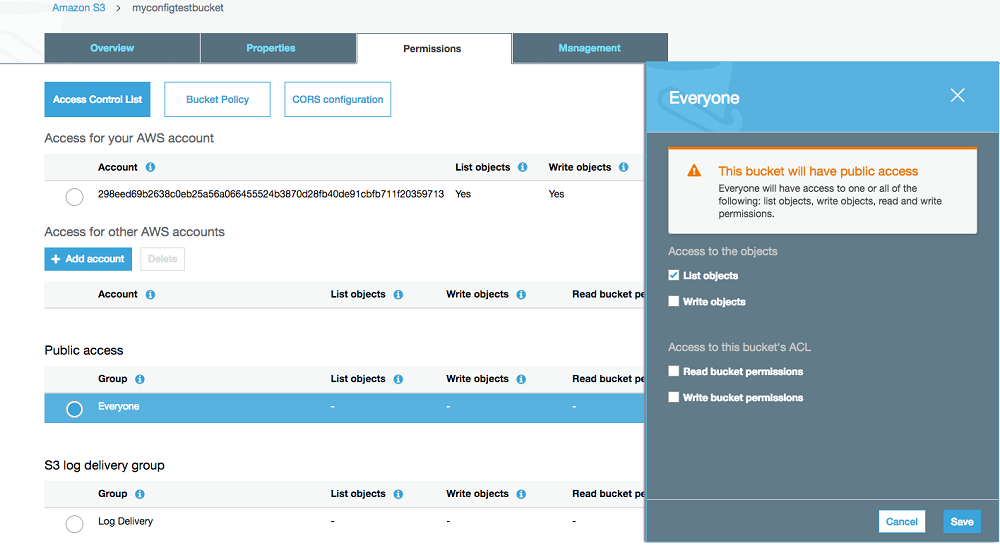
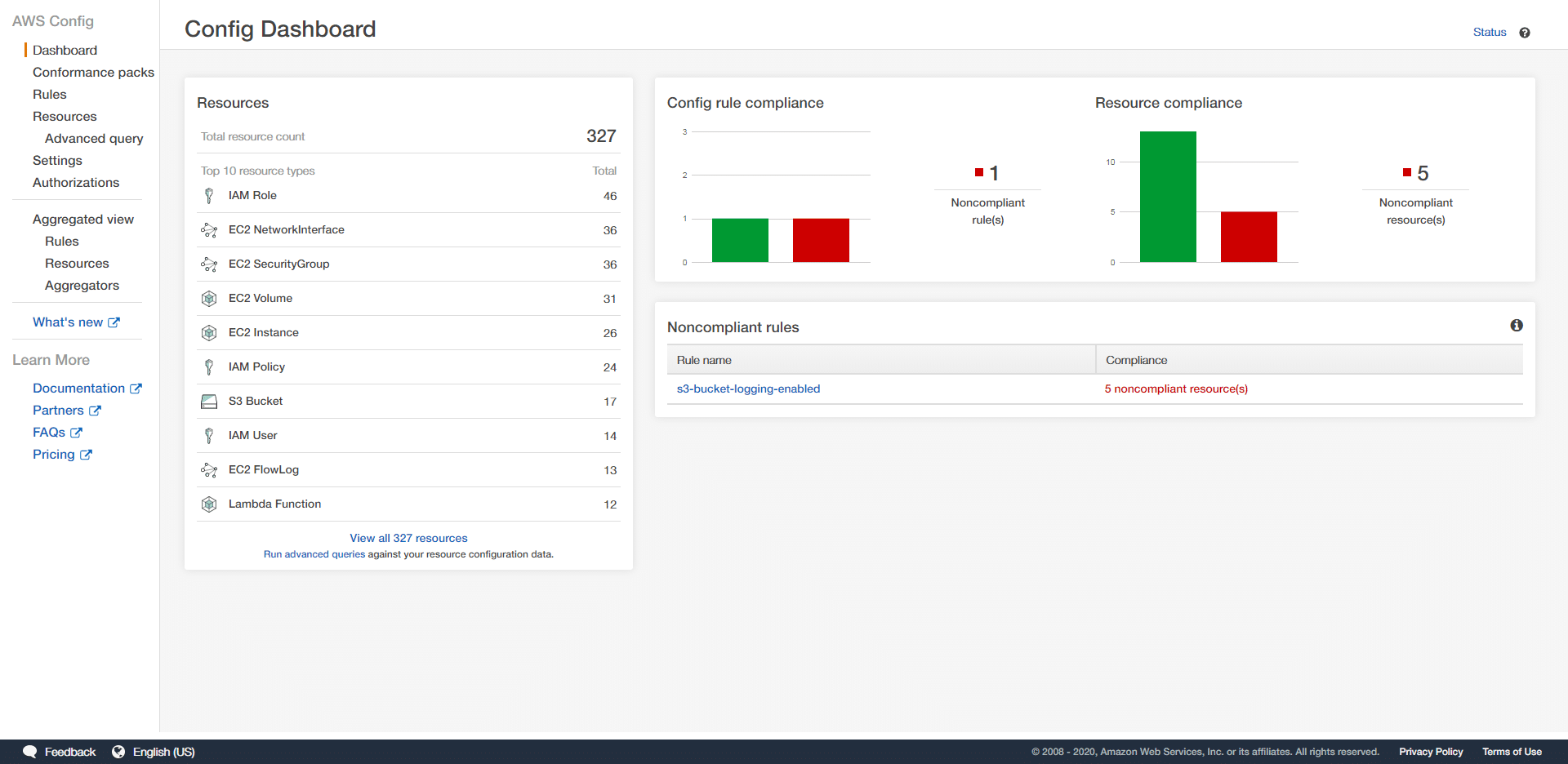
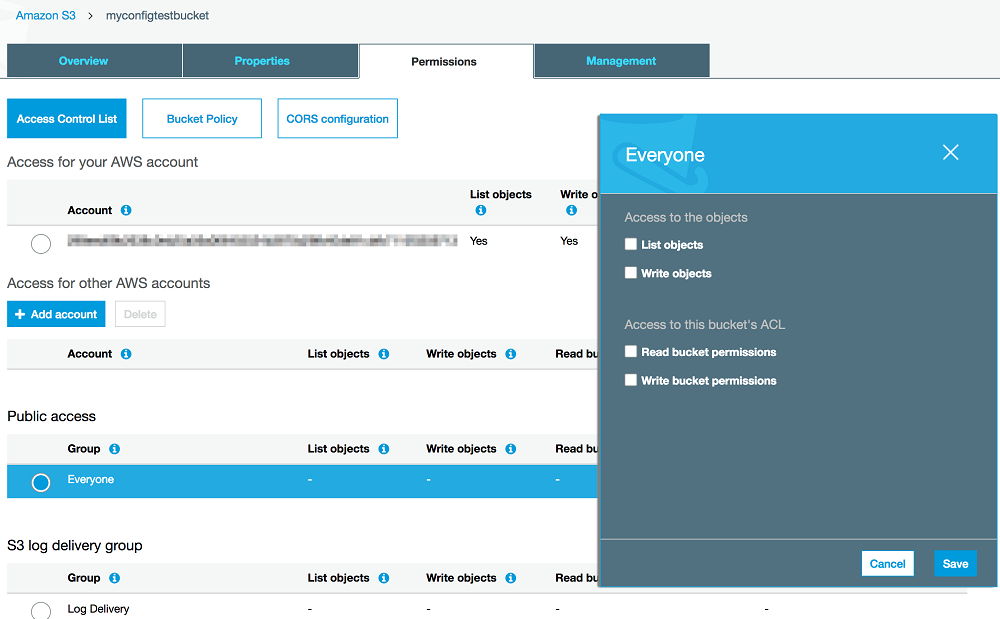
How to Use AWS Config to Monitor for and Respond to Amazon S3 Buckets Allowing Public Access | AWS Security Blog

How to Use AWS Config to Monitor for and Respond to Amazon S3 Buckets Allowing Public Access | AWS Security Blog

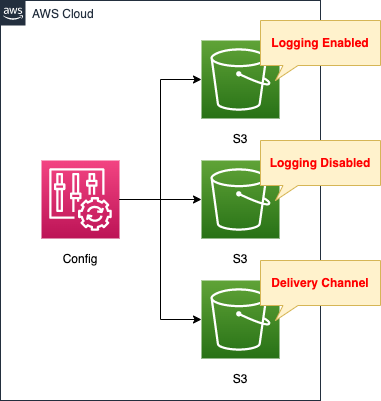
Example Scenarios for AWS Config Continuous Monitoring of Amazon S3 Bucket Access Controls | AWS Cloud Operations & Migrations Blog

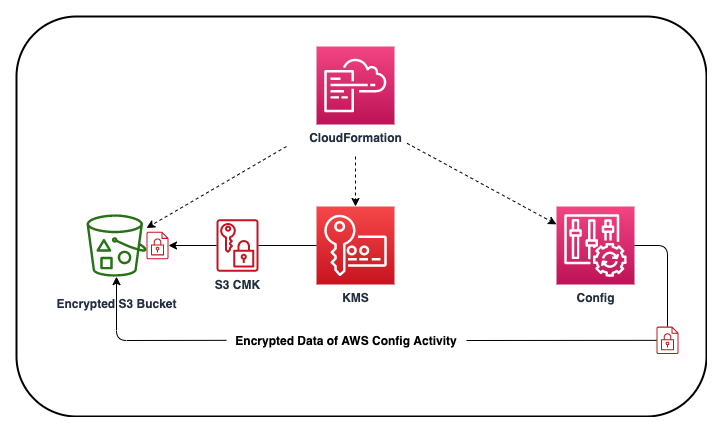
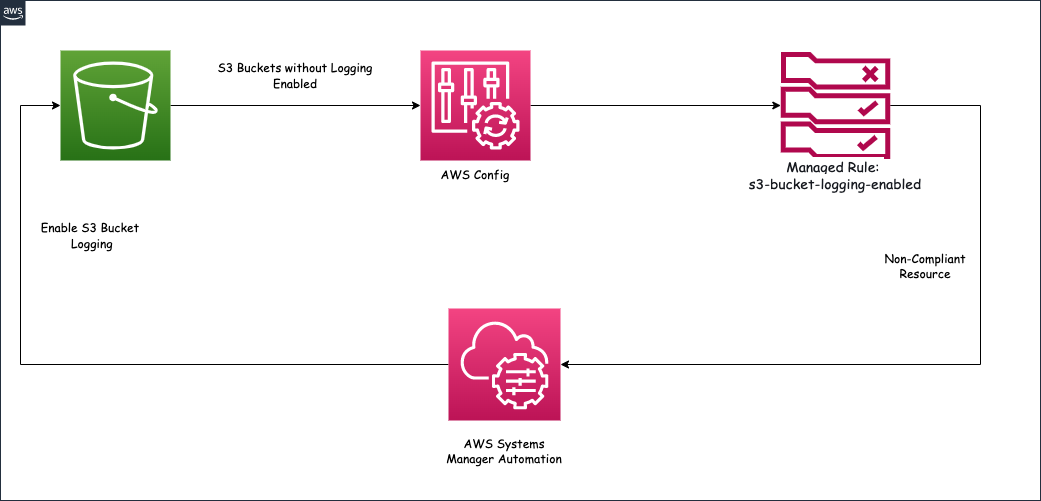
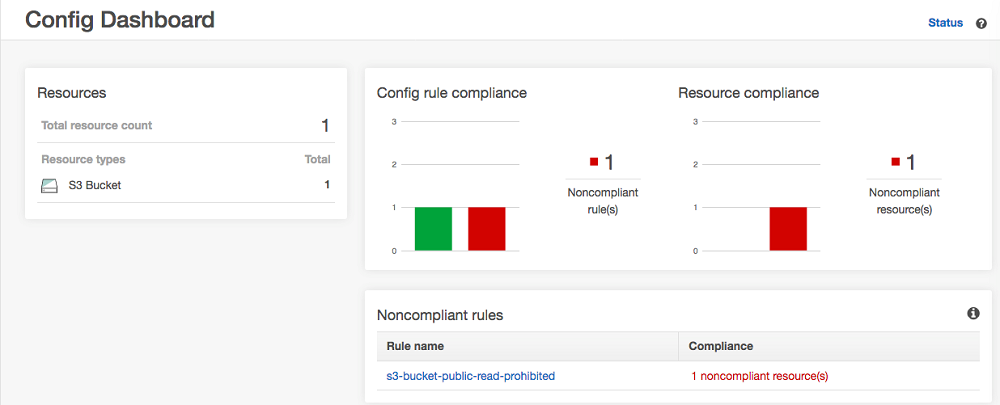
Amazon S3 bucket compliance using AWS Config Auto Remediation feature | AWS Cloud Operations & Migrations Blog

Amazon S3 bucket compliance using AWS Config Auto Remediation feature | AWS Cloud Operations & Migrations Blog